JumpCloud has added Conditional Access policies to its Directory Platform, enabling IT admins to adopt Zero Trust security from the same cloud platform that they use to manage and securely connect users to IT resources.
Conditional Access is policy-driven control that ensures only appropriate users from known networks, known devices and with appropriate privileges, be granted access to company resources. With this release, the folks at JumpCloud say they’re making it easier for IT teams to adopt a “never trust, always verify” model in their organization.
According to the August 2020 Forrester Research, Inc. blog post, A Look Back At Zero Trust: Never Trust, Always Verify, “Old-school approaches to security aren’t cutting it. Many organizations feel that Zero Trust is too hard, time-consuming, or costly to implement, but it will save your organization in the long run. The strategy leads to the reduced risk of being the victim of a ransomware attack, paying hefty fines, or suffering loss of customer trust following a breach.”
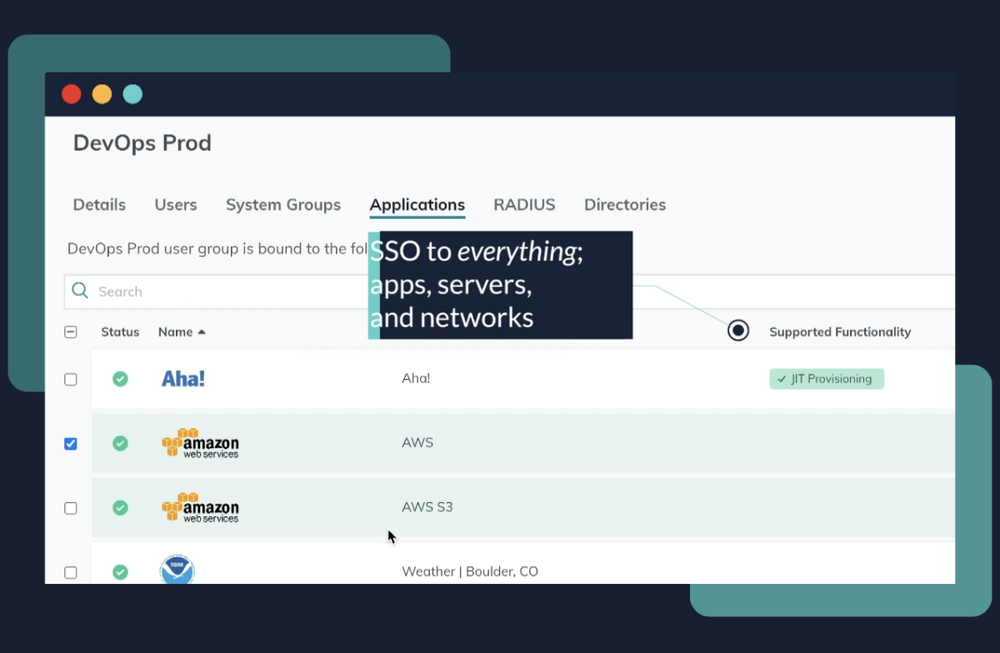
The JumpCloud Platform’s identity and access control provides core authentication and authorization to employee devices, networks and on-premise and cloud applications. The release of Conditional Access introduces policy-driven security checks to confirm authentications are verified via trusted networks and devices managed by the organization, giving JumpCloud customers an easier path to implement a Zero Trust model, says Brian Coleman, founder of MatchstickBHM.
“With JumpCloud’s new Conditional Access policies, we can strengthen our Zero Trust posture with trusted identity, network, and device, and manage it through a single admin portal,” he adds.
The folks at JumpCloud say the company’s Conditional Access includes four main components to support Zero Trust:
-
Identity Trust: JumpCloud’s core directory securely manages an organization’s user identities including all credential control and revocation, two factor verification and contextual data to ensure appropriate levels of permission when accessing resources.
-
Network Trust: JumpCloud’s Network Trust enables organizations to ensure authentication requests are only allowed from specific IP addresses or ranges of addresses. This restricts traffic to resources only from locations organizations know or otherwise ‘trust’.
-
Device Trust: JumpCloud’s Device Trust ensures that employees only access company resources from devices which are under company management, and secured through JumpCloud’s MDM and agent-based management functions. The new Conditional Access release adds the ability to more granularly define what constitutes a trusted device and prevent or allow authentication based on policy and context.
-
Policy Driven Access Control: Tying these new identity, network and device trust functions together are new simple-to-implement access control policies. The policies provide a customizable and layered approach enforcing second factors of verification (MFA) when combinations of network and/or device are deviating from the gating policy.
JumpCloud’s Conditional Access policies are available now as part of the JumpCloud Platform Plus package, and can also be added a la carte to other packages.
